On July 15th, Twitter accounts of major US tech figures, companies, politicians and celebrities, including Elon Musk, Barack Obama, and Bill Gates, and Apple were hijacked in what turned out to be one of the biggest attacks in the history of the social network. According to Twitter Support, this was a “coordinated social engineering attack by people who successfully targeted some of their employees with access to internal systems and tools.”
Twitter immediately froze certain the affected accounts and removed Tweets posted by the attackers. It also limited functionality for a much larger group of accounts, such as all verified accounts (even those with no evidence of being compromised), while it investigated the attack. The social media giant found “no evidence that attackers accessed passwords.” Out of “an abundance of caution”, and as part of the incident response, Twitter also took the step to lock any accounts that had attempted to change the account’s password during the past 30 days.
David Higgins, Technical Director, CyberArk, commented: “After initially looking like successful social engineering of some key insiders enabled this external hack , there is some talk that more ‘traditional’ methods were used to buy inside cooperation and access to the admin tool that allowed takeover of high profile accounts. Either way, it shows that hackers will always target the privileged access and rights of insiders. In some cases this is through identity takeover but it’s possible that in this case we see an example of the malicious insider at work.”
Attack method
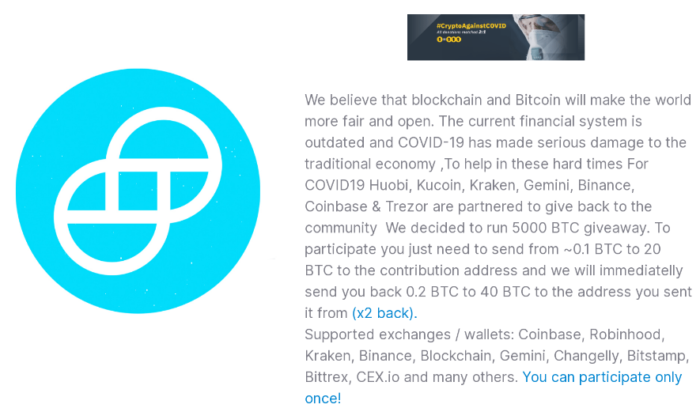
The attackers gained access to several high-profile accounts and tweeted about a cryptocurrency giveaway on their behalf. The messages posted by the attackers promised to double any payments made to a BTC address.
Cybersecurity company Group-IB’s threat researchers identified two cryptocurrency wallets (bc1qxy2kgdygjrsqtzq2n0yrf2493p83kkfjhx0wlh and bc1qwr30ddc04zqp878c0evdrqfx564mmf0dy2w39l) posted by the attackers and establish that in just hours they’ve collected more than 13.4 BTC (SGD 169,000). The total number of transactions associated with these two wallets is 416 (at the moment). The first transaction was registered at 3:03 AM Singapore time on July 16th.
According to Group-IB’s CEO Ilya Sachkov, the attackers have chosen the most straightforward way possible to capitalize on the level of access they’d gained. “This could have ended far worse affecting the stock market heavily or even resulting in a geopolitical catastrophe. This is the least they could have done with the God-mode access they had.
“This attack has demonstrated again a huge problem of low financial literacy and bad cyber hygiene. There ain’t no such thing as a free lunch, it’s as simple as that. Anyone who promises you to double your payment and asks for an advance fee is a scammer. Think twice before you transfer your money or confidential personal data,” says Sachkov.
According to Check Point Software, compromised accounts of large cryptocurrency exchanges and leaders in the cryptocurrency community even claimed to be partnering with a made up organisation called “CryptoForHealth”:

The website mentioned in those tweets, cryptoforhealth[.]com, was registered on the same day of the attack and claimed to be helping the community after the financial losses caused by COVID-19. In reality, the website was asking for bitcoin to be sent to the same wallet address that appeared in the tweets.
Incident takeaways
“I think there are two major takeaways from this incident. First, users need to be aware of scams and stay cautious on social media; they need to be able to recognize them. Second, we need to be extra careful with our online assets—anything critical has to have, at a minimum, two-factor authentication,” commented Dmitry Galov, security researcher at Kaspersky.
For Galov, “this major scam highlights the fact that we are living in an era when even people with computer skills might be lured into scammers’ traps, and even the most secure accounts can be hacked”. Kaspersky estimates that during the two hours of the attack, at least 367 users transferred around 120,000 dollars in total to attackers.
Kaspersky recommends a thorough review of the apps that have access to Twitter accounts, which can be found in the Twitter account settings. Galov suggests revoking access to your account from all of them, or the ones that you don’t consider thoroughly protected, so that, in the event of a hack, your account can’t be reached.
According to CyberArk’s Higgins, this [hack] demonstrates the importance of placing strong controls and monitoring over those users that have privileged access to key systems and services. He reckons that it’s a clear reminder of why social media – which has emerged as a critical communications conduit – should be treated by companies as critical infrastructure and secured as such.
Michael Borohovski, Director of Software Engineering at Synopsys Software Integrity Group, points at far more sinister possibilities in light of the attack.
“Given that numerous high-profile Twitter accounts were compromised as part of this attack — accounts that would presumably be protected by multifactor authentication and strong passwords — it is highly likely that the attackers were able to hack into the back end or service layer of the Twitter application. Indeed, some of the accounts (Tyler Winklevoss, for example) have confirmed they were using multi-factor authentication and got hacked anyway. If the hackers do have access to the backend of Twitter, or direct database access, there is nothing potentially stopping them from pilfering data in addition to using this tweet-scam as a distraction, albeit a very profitable one. We haven’t seen data on this, and won’t until a post-mortem is released by Twitter, but it’s a possibility,” he said.