After Optus and Medibank, another listed Australian firm has been hit by cybercriminals.
Digital payments firm Latitude Financial, in a March 16 announcement, said it “has detected unusual activity on its systems over the last few days that appears to be a sophisticated and malicious cyberattack.”
On March 20, the company confirmed that it was indeed a “sophisticated, well-organised, and malicious cyberattack which remains active.”
What went down
The data breach was believed to have originated from one of Latitude’s major vendors, the company said.
Before the incident was isolated, the attacker managed to get hold of Latitude employee login credentials, which was then used to steal data held by two other service providers.
Approximately 103,000 identification documents, of which 97% are copies of driver’s licences, were stolen from the first service provider, while 225,000 customer records were taken from the second service provider.
Latitude said it is working with the Australian Cyber Security Centre, as well as several relevant law enforcement agencies and cybersecurity specialists in response to the attack.
“Our priorities are to ensure the ongoing security of our customers, our employees and our partners while continuing to deliver services,” the company said in its March 16 statement.
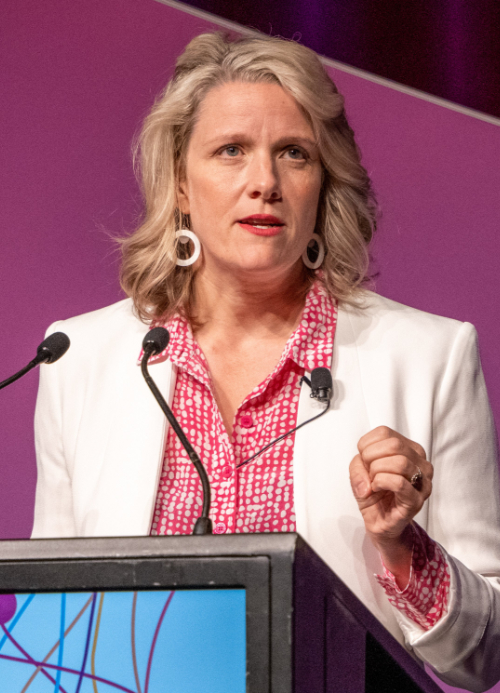
Clare O’Neil, Australian Minister for Home Affairs and Minister for Cyber Security, confirmed in a series of tweets that Latitude is cooperating with the ACSC and regulators “to minimise the damage resulting from (the) incident,” and has reminded “everyone in the community to be vigilant about their personal cybersecurity.”
The Minister also urged the public to make use of all the tools and advice available at the ACSC website.
As of March 20, the attack on Latitude remains active, prompting the company to take its platforms offline. As a result, customers and merchant partners cannot currently be serviced, while onboarding of new customers is similarly halted.
“We cannot restore this capability immediately, however we are working to do so gradually over the coming days and ask our customers for their continued patience. Our restoration of these services is aligned to our forensic review,” the March 20 statement read.
Crisis time
Getting down to brass tacks, Latitude also disclosed that less than 4% of the stolen data were copies of passports or passport numbers, and that less than 1% were Medicare numbers.
“As our review deepens to include non-customer originating platforms and historical customer information, we are likely to uncover more stolen information affecting both current and past Latitude customers and applicants. We will provide a further update when we have more information to share,” Latitude said in its March 20 statement.
“Latitude encourages our customers to remain vigilant. We will never contact customers requesting their passwords,” the statement further read.
After informing its customers about the cyberattack through an email on March 16, the company said it began contacting affected customers and applicants on March 20.
Each customer and applicant will be notified which personal information had been stolen from them, what the company is doing to support them, and what additional steps customers should consider to further protect their information, Latitude said.
The company added that it is working with relevant government agencies to replace identification documents, where necessary, at no cost to customers.
Further, Latitude said it has also engaged IDCARE, a not-for-profit organisation, and Australia and New Zealand’s national incident response service, specialising in providing free, confidential cyber incident information and assistance.
Dedicated contact centres were also established for affected Latitude customers in Australia and New Zealand, alongside a dedicated help page on the company’s website.
While Latitude is still assessing the anticipated total cost of the cyberattack to the company, it has committed to a review of the incident once it is contained.
Ahmed Fahour, the company’s CEO, has apologised to customers and partners “for the distress and inconvenience (the) criminal act has caused.”
“Our focus is on protecting the ongoing security of our customers, partners and employees’ personal and identity information, while also doing everything we can to support customers and applicants who have had information stolen,” he said.
“While we continue to deliver transactional services, some functionality has been affected resulting in disruption. We are working extremely hard to restore full services to our customers and merchant partners and thank them for their patience and support. We understand their frustration. Customers should refer to Latitude’s website for regular updates,” the Chief Executive added.
Security flaws
Cybersecurity experts have taken a closer look at the Latitude Financial data breach, and everyone seemed to agree on one thing — there is no room for complacency in the face of cyberthreats that are only growing in sophistication.

According to Phillip Ivancic, APAC Head of Solutions Strategy, Synopsys Software Integrity Group, the incident indicates a worrying trend of cybercriminals moving to a business model of selling Australians’ highly sensitive personal information, including biometric information, on the dark web.
“What’s most disturbing about the Latitude Financial attack is that at least 100,000 facial images, matched with full drivers’ licence details, were stolen. Australians can change passwords and monitor credit reports, however, they can’t change the biometric markers on their face,” he said.
“Losing control of biometric information which is already matched with government-issued identity documents like driver’s licences, is particularly worrying in the age of AI and deepfakes, and could result in a steep increase in future fraud,” Ivancic continued.
The cybersecurity expert also noted the likelihood of missing or insufficiently tested cybersecurity controls, due to the fact that the hackers got in via compromised credentials used by Latitude’s third-party vendors.
Clearly, the cyberthreat landscape is growing more complex, with data breaches capable of crippling organisations’ IT infrastructure for months, warned Phil Walsh, Regional Vice President – ANZ, ForgeRock.

“Passwords are the weakest point of entry for attackers in these situations. Phishing, malware, ransomware, and credential-based attacks are targeting passwords more than ever before, making them the most vulnerable part of digital identity authentication,” he explained.
To this end, businesses should embrace secure, frictionless passwordless authentication methods that remove the need for employees to interact with passwords, Walsh said.
“Passwordless authentication replaces traditional passwords with a more user-friendly, secure method that includes tokens, certificates, authenticator apps, or biometrics. These methods can be combined for passwordless multi-factor authentication (MFA), which offers the highest level of user authentication security,” the ForgeRock executive continued.

While Australian banks are some of the most digitally advanced in the world, the right tools are insufficient without the “right processes in place across the board to make cybersecurity an organisation-wide effort,” noted Sean Duca, Vice President and Regional Chief Security Officer, Asia Pacific & Japan, Palo Alto Networks.
Duca urged Latitude’s customers to remain vigilant against phishing or social engineering attacks, emphasising that the threat to the company is still ongoing.
“It is recommended to keep an eye on your social media accounts for any suspicious activity. Read your card and monitor your bank account statements closely for any unusual transactions,” he said.
Phillip Ivancic of Synopsys stated that the Latitude data breach could have been prevented if several standard cybersecurity controls had been implemented. These controls include:
- Encryption combined with strong key management for sensitive information such as driver’s licences and facial biometrics. This ensures that third parties cannot access sensitive ‘in the clear.’
- Effective implementation of MFA rather than relying solely on usernames and passwords for third-party access.
- Designing application business logic to limit a third party’s access to sensitive data from the outset and prevent mass exfiltration of such data.
“Before sharing any data with a third party, a threat model or architecture review should be conducted on the project to map out how the data flows will work, and the security controls that will need to be in place to prevent such attacks. There are many frameworks for identifying the range of security controls that need to be in place, including Australian government resources from the ASD (Australian Signals Directorate). Threat modelling techniques will help identify the appropriate controls for each project and are especially important where data is shared between third parties,” Ivancic explained.
He added that penetration testing can ensure that the chosen controls are effective and can withstand sophisticated attack techniques. Automated and continuous dynamic application testing, said Ivancic, can ensure that important controls remain effective between manual, expert-led penetration testing.
Far from over
As of press time, the Latitude Financial incident has yet to be resolved. While the company has been as transparent as it could be about what happened, customers’ personal data are still out in the open.
What the hackers intend to do about it is still unknown.
Meanwhile, another Australian company has been hit by a cyberattack almost the same time as Latitude. IPH, an international intellectual property services group, said it has “detected unauthorised access to a portion of its IT environment” on March 13.
Investigation is currently underway to determine whether information stored in the compromised systems were accessed by an unauthorised third-party.
Australia has recently been ranked first in the world among countries with great progress and commitment to enhancing cybersecurity, according to an MIT study.
Meanwhile, during her keynote address at the 2023 Australian Information Security Association’s Australian Cyber Conference in Canberra, Cybersecurity Minister Clare O’Neil said the government is hard at work building a strong cyber defence around the country, in order to make Australia “more resilient to current and future cyberthreats.”
The minister also expressed confidence that Australia can be the most cyber-secure country in the world by 2030. However, the effectiveness of such a goal depends on the outcome of ongoing cybersecurity challenges faced by companies like Latitude Financial.
















