When the Log4Shell vulnerability hit millions of servers and applications that used Java software a year ago, IT teams everywhere scrambled to find a way to plug the loophole. One big challenge was looking for instances where the widely used Java-based logging component (Log4j) might be present and thus open to a cyberattack. The problem was that there were so many places to look, making it a difficult task for most IT teams, even those that had the scale to speed up the process.
There’s a better way. Instead of simply looking for the presence of components such as Log4j, organisations should find where they are run. This way, they can more precisely manage the issue. This highly accurate runtime-level visibility is now available with Azul Vulnerability Detection, a new software-as-a-service (SaaS) offering that continuously detects known security vulnerabilities that exist in Java applications. By offering unrivalled visibility, it enables faster remediation of vulnerabilities with significantly less operational overhead.
More precision and visibility
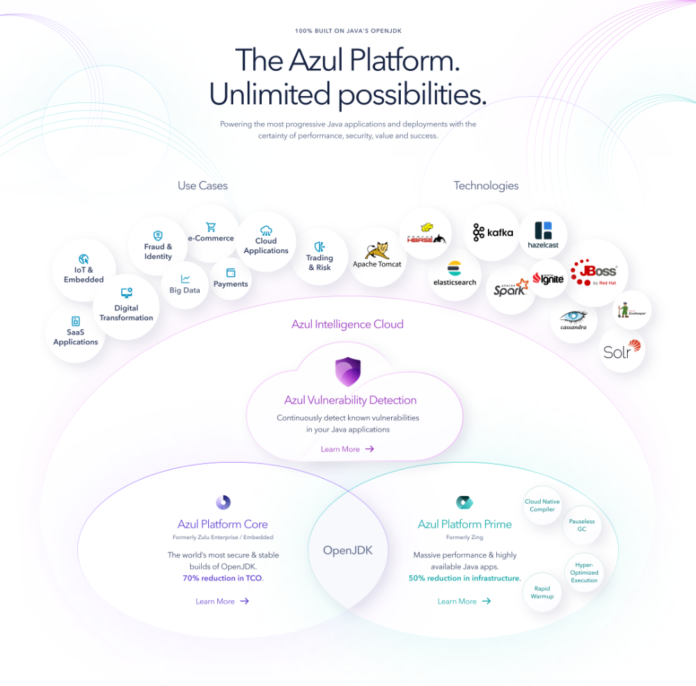
Azul Vulnerability Detection is created by Azul, the only company 100% focused on Java. With a 20-year heritage of Java leadership, Azul provides a Java platform for modern cloud enterprises that is trusted by millions of Java developers, hundreds of millions of devices and the world’s most highly regarded businesses.
The new Azul Vulnerability Detection, an agentless cloud service, helps organisations understand their Java application exposure to known vulnerabilities based on real usage in production, QA, and development. It is ideal for in-production use and addresses the rapidly increasing enterprise risk around software supply chain attacks.
By 2025, 45% of organisations worldwide will have experienced attacks on their software supply chains, a three-fold increase from 2021, according to research firm Gartner. At the same time, vulnerabilities in third-party production code, which is common in today’s complex IT environment, continue to increase the risk of exposure for enterprises.
An estimated 40% to 80% of the lines of code in software today come from third parties such as libraries, components, and SDKs. Whether commercial or freely available open source, they present a growing risk to all enterprises and need addressing across all phases of the software supply chain.
To do this, Azul Vulnerability Detection identifies the code run using sophisticated, highly granular techniques inside Azul JVMs and maps against a curated Java-specific database of common vulnerabilities and exposures (CVEs). This produces more accurate results and eliminates false positives, even for custom code and shaded components.
Additionally, the history of detections is retained so that when new CVEs are disclosed, organisations can find out when and on what systems they have been running the vulnerable versions. This allows for focused and efficient forensics. Users can access data about which components are (or were) present, in use and vulnerable, via either the product’s API or an intuitive user interface.
Gain agility while toughening up security
Azul Vulnerability Detection has wide compatibility. It works with any Azul JVM (including free Azul Zulu Builds of OpenJDK) and is compatible with all Java applications, libraries, and frameworks. Since it is agentless, it also avoids the performance penalty associated with other tools that require customers to install and manage a separate piece of software. By offering ongoing detection on code that is actually running, it enables organisations to focus on production – the critical end step of the software supply chain.
Together, these features will help boost security while enabling organisations to operate at speed, taking advantage of the business agility that is critical to competing effectively today.